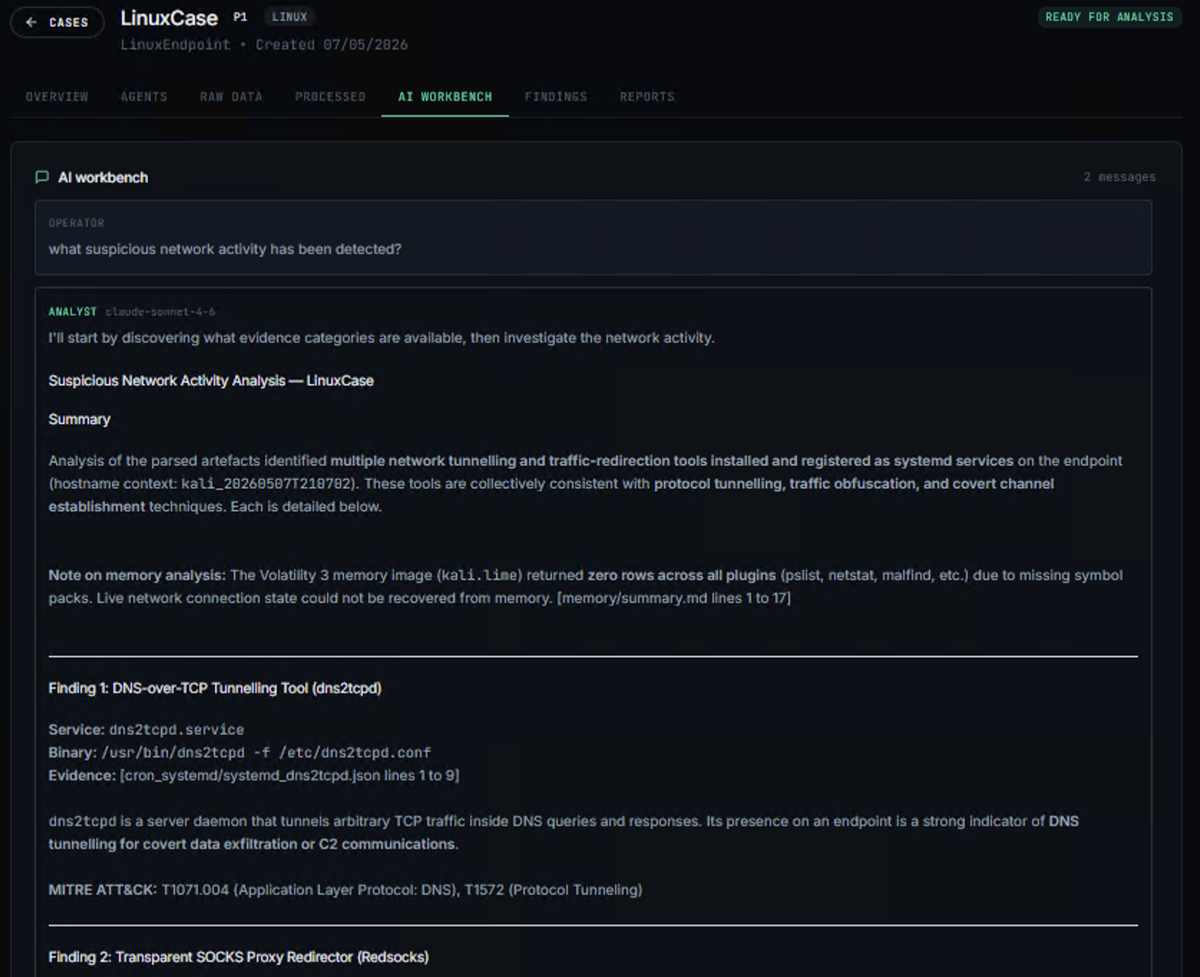
The full investigation lifecycle. On your appliance.
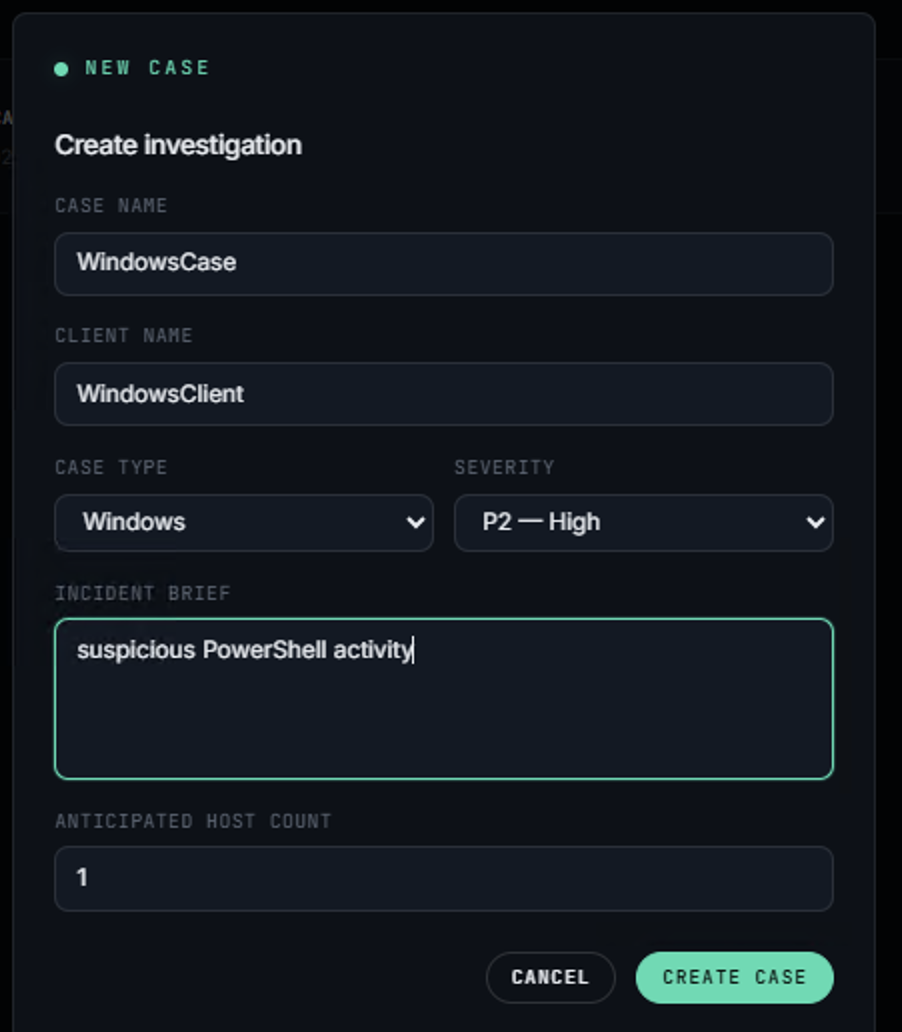
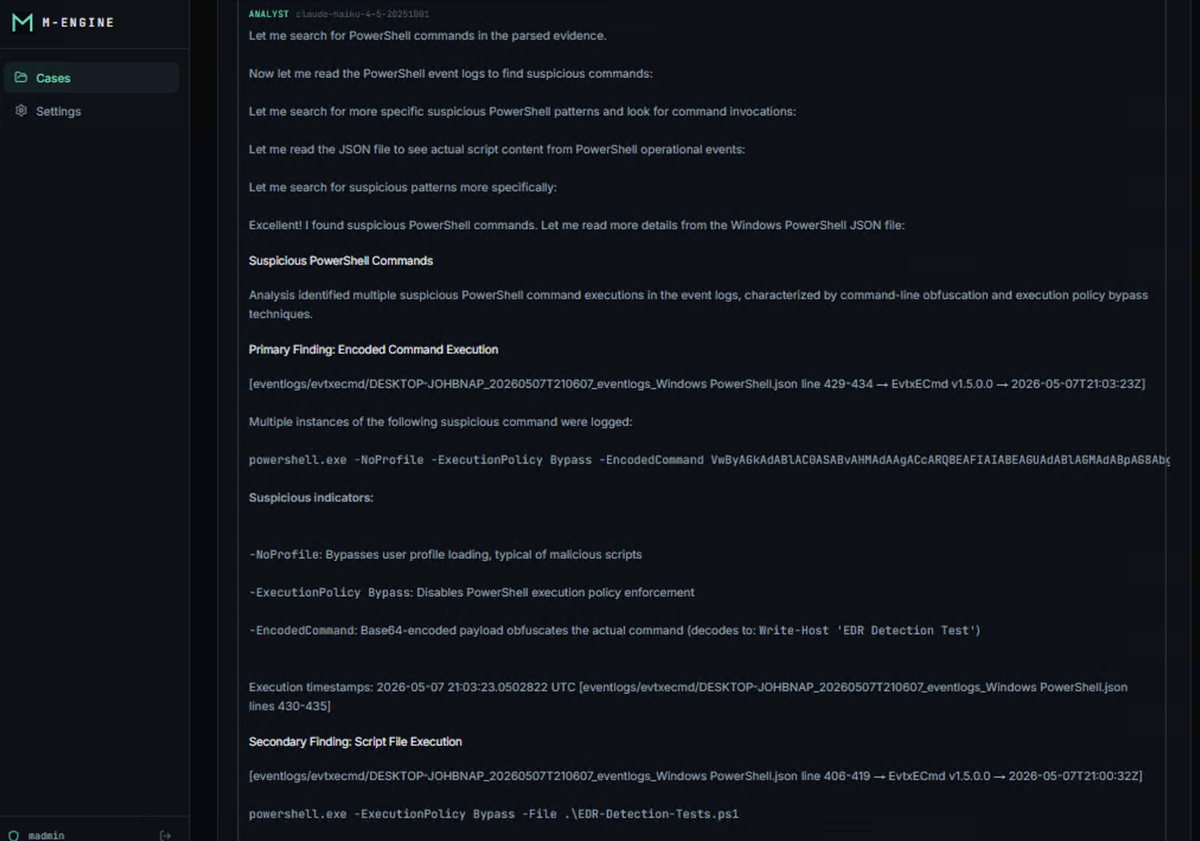
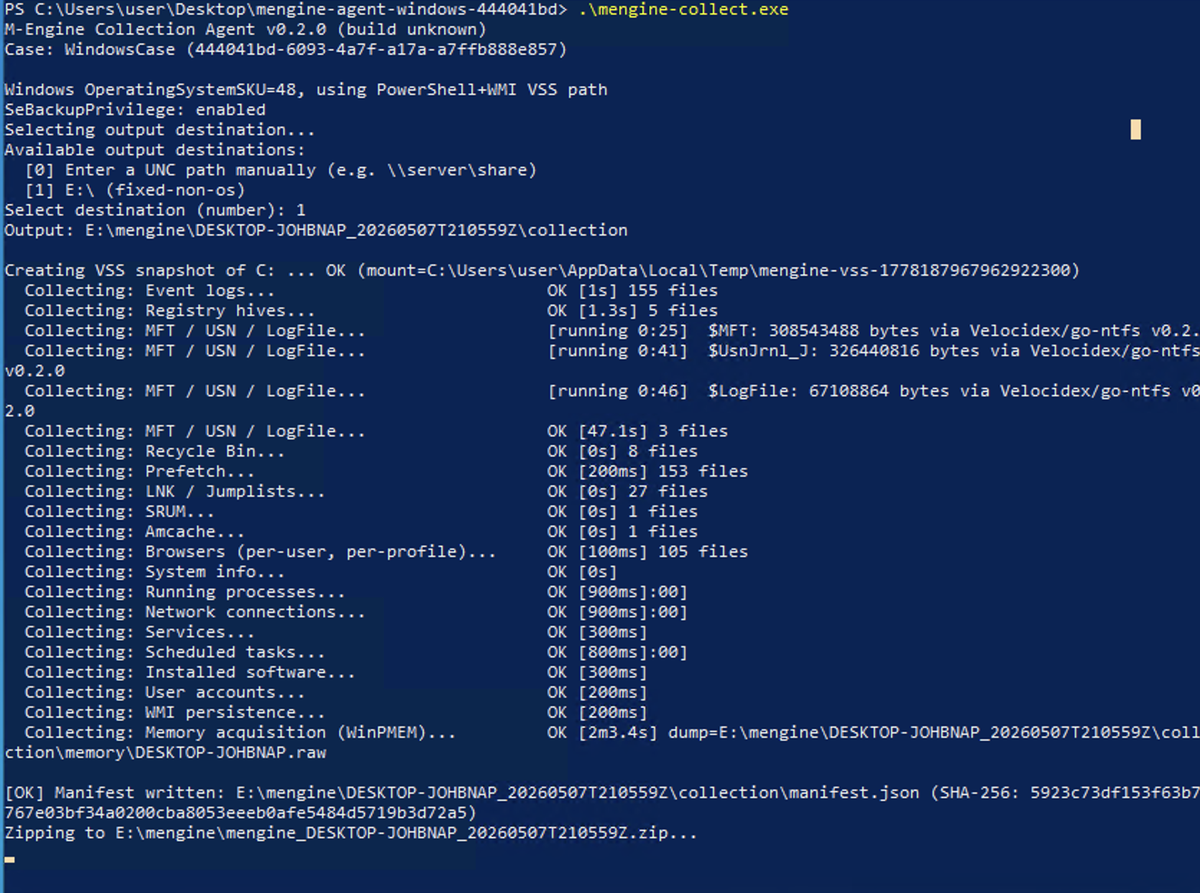
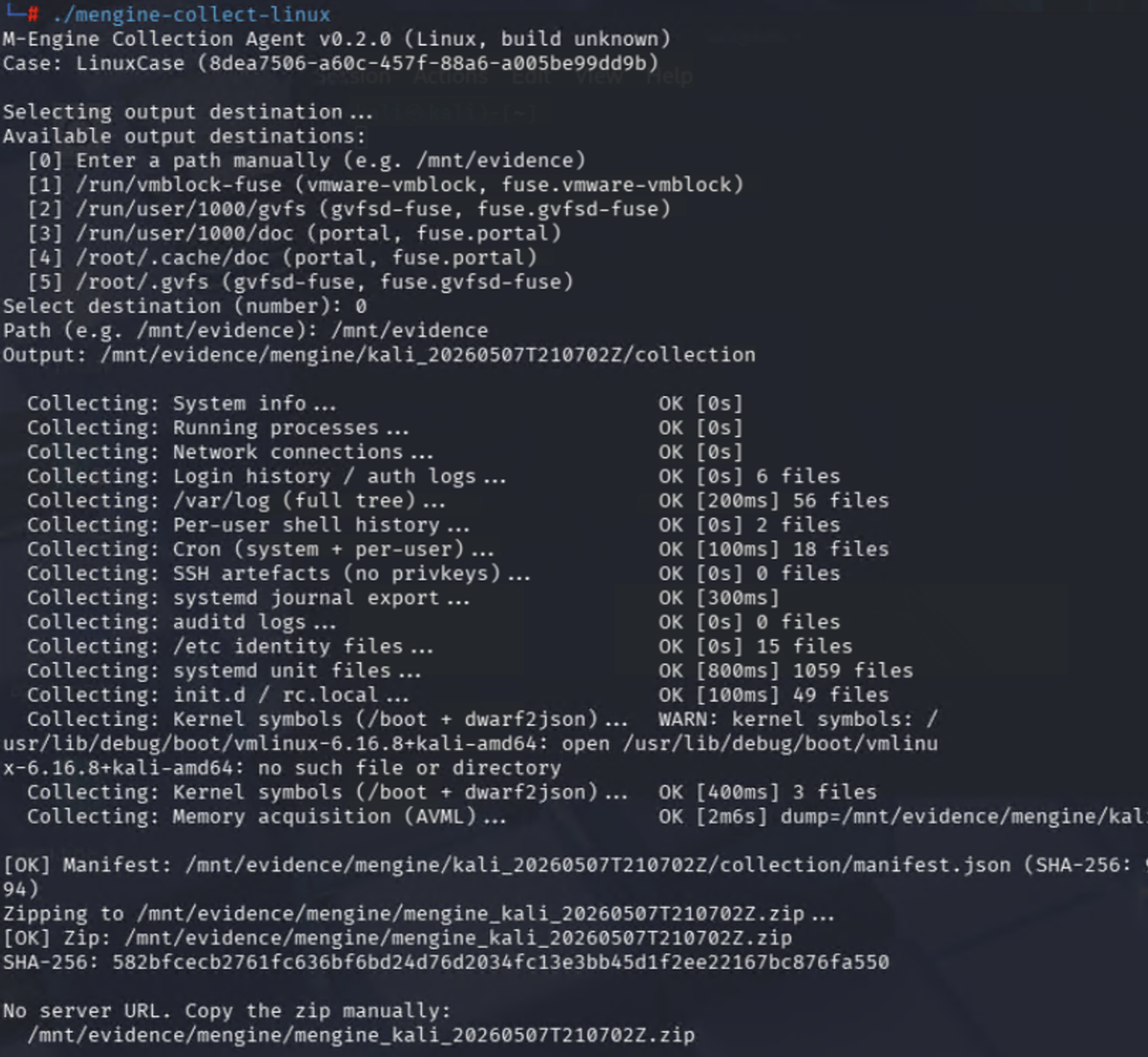
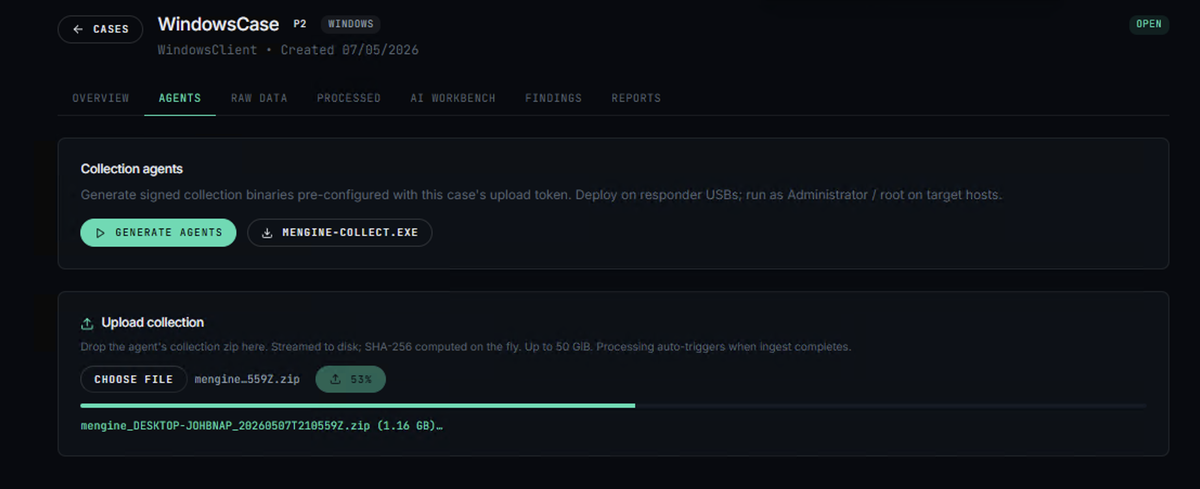
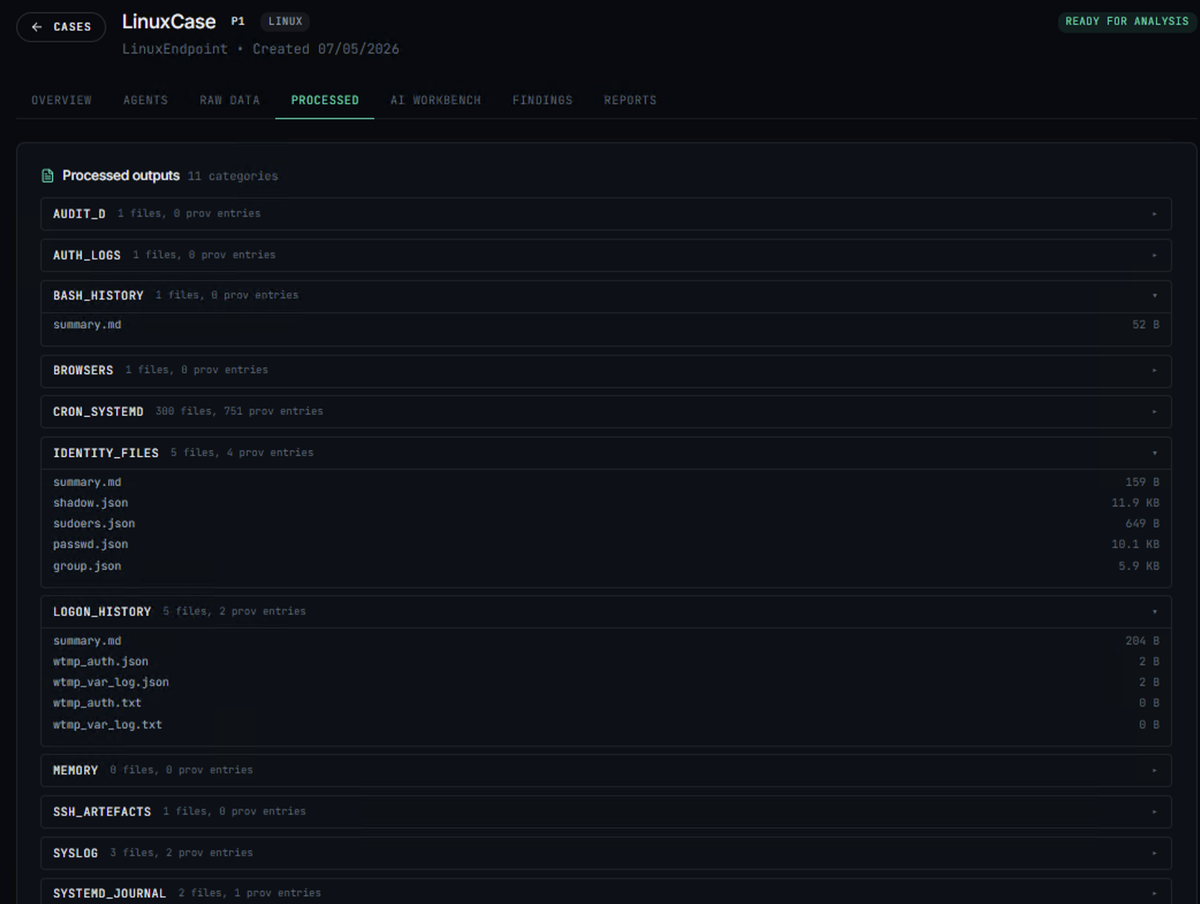
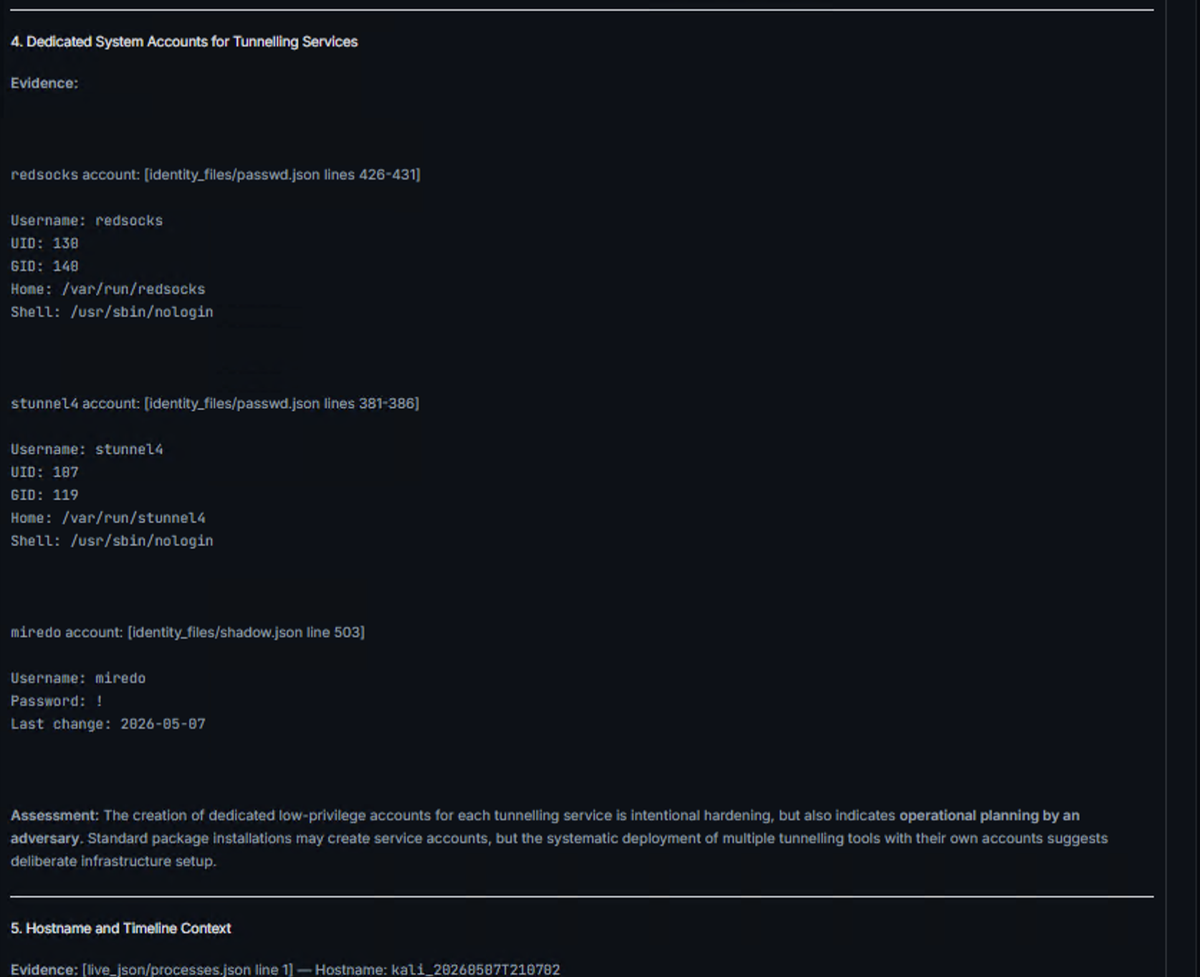
Stand up M-Engine on a single VM in your environment. Generate a per-case collection agent. Run it as administrator on the host you are investigating. The engine ingests, processes, analyses, and writes the report.
Nothing leaves your network unless you choose to enrich with external threat intelligence using your own keys.